Introduction - Welcome to Microkeeper
Welcome to Microkeeper! Our guides are here to introduce and educate you, setting you up for a successful new Microkeeper experience.
This opening page provides a roadmap through all the key areas of the system. Have fun exploring!
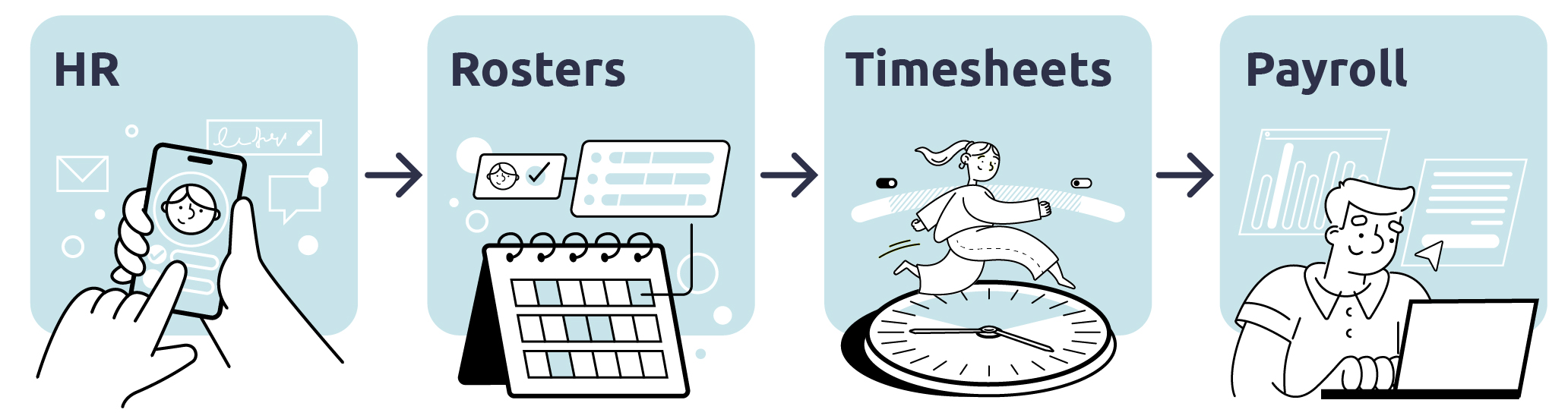
What is Microkeeper?
Microkeeper is a comprehensive end to end employee management and payroll system designed to streamline, simplify and empower Australian businesses.
Within Microkeeper, there is 4 core modules:
- Cloud HR
- Rosters
- Timesheets
- Payroll
This guide will provide you with an overview of the main modules in Microkeeper and their functionalities, helping you to navigate the system and make the most of your new journey!
Cloud HR
The Cloud HR module is the foundation of your workforce management, allowing you to:
- Digitally Onboard New Employees - Integrate new team members with a digital onboarding experience. Allow new staff to self onboard themselves, digitally sign contracts and upload key documentation with a self-service online portal.
- Manage Employee Records - Maintain an organised and secure database of employee information.
- Leave Management - Efficiently handle leave requests and manage absence tracking which will automatically process the requests into your payroll.
Rosters
The Roster module enhances the scheduling and management of your employees planned work hours with features that can:
- Create and Manage Shifts - Easily create and assign shifts to employees, accommodating optimal staffing needs and employee availability through advanced analytics. Advanced scheduling features allow you to quickly fill empty shifts and make updated adjustments in real time.
- Roster Automation - Automatically fill eligible staff to open shifts, taking into account their availability, skill, experience and approved overtime.
- Time and Attendance Integration - Seamlessly integrate with the Timesheet modules for easy tracking of work hours and attendance
- Employee Self-Service for Shift Preferences - Empower employees with the ability to set their availability and preferential shifts through their online portal.
Timesheets
The Timesheet module simplifies time and attendance tracking of worked hours with:
- Multiple Clocking Options - Capture and manage employee timesheet data with a variety of clocking options such as Mobile clocking, Location restriction clocking, Facial Recognition, Fingerprint scanners and NFC tags.
- Digital Time Tracking - Record and store accurate timesheets through our time tracking software, eliminating errors in recording data allowing for review wherever you have web access.
- Seamless Payroll Integration - The timesheet module integrates seamless with the Payroll module, allowing for automating the calculation of wages based on hours worked, time of day and much more.
Payroll
The Payroll Module simplifies the complex process of payroll management, enabling:
- Integrated Payroll - Direct integration with all the modules in Microkeeper, the payroll can factor in new hire info, hours worked, breaks, rosters and more to create a comprehensive payroll experience.
- Payroll Automation - Powerful payroll automation that can be customised so you spend less time processing payroll and more time doing what you want to do!
- STP Compliant - Fully integrated with the ATO's STP Phase 2 requirements, making sure your business is compliant with the Australia Government requirements
- Payroll Reporting - Get detailed reports that offer a breakdown of costs, taxes, deductions, entitlements, changes of payrates, super, jobs, superannuation and more.
Getting Started with Microkeeper
It's best to work through the guides with your own account. You can register for a free account through our Sign Up page here.
Once you have signed up, login and let us get your business started with Microkeeper.
As you navigate through Microkeeper you will notice our info dots. Mouse over them for additional information throughout the Microkeeper system.
i The black info dot is used to provide you with additional information throughout the Microkeeper System
Supported Setup Process with Microkeeper Specialists
If following guides and self onboarding your business account isn't your thing, our team at Microkeeper offer a supported setup process to make the move as seamless as possible
Check out our Supported Setup and Training page here for more information.